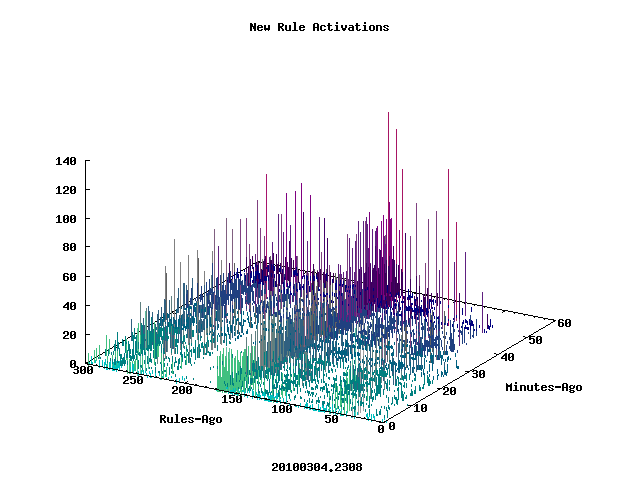
Those trixy blackhatzes are making a real mess of things these days. The last day or so in particular has been a festival of hacked servers and exploited free-hosting sites. Just look at this graph from our soon-to-be-launched Spam-Weather site:
While spammers have always enjoyed exploiting free services they have been particularly busy at it the last few days. The favorites this time around have been webstarts and doodlekits. What makes sites like these so attractive to the blackhats is that there is virtually no security on the sites. Anybody can sign up for a new account in minutes without any significant challenges. This means that the entire process can be scripted and automated by the blackhats.
After they’ve used one URL for a while (and it begins to get filtered) they simply light up another one, and so on, and so on.
Some email administrators are tempted to block all messages containing links to free hosting sites — and for some that might be an option — but for PROs like us it’s not. There are usually plenty of legitimate messages floating around with links to free-hosted web sites so blocking all such links would definitely lead to false positives (unacceptable).
At ARM we have a wide range of defenses against these messages so we’re able to block not only on specific links but also on message structures, obfuscation techniques, and other artifacts that are always part of these messages. In addition to that our tools also allow us to predict what the next round of messages might look like so that even when they do change things up we’re often ahead of them.
No mistake about it though… it’s hard work!
It would be _MUCH_ better for everyone if folks that offer free hosting and other commonly exploited services (like URL shortening, blog hosting, and free email accounts) would do a better job keeping things secure.
I’m looking forward to the new site, Pete! I always appreciate your graphs and running commentary.
And you and the sortmonsters must be doing a great job, I haven’t seen the adult campaign you referenced.
Thanks! I’ll pass that along. 🙂
We’re looking forward to getting the new site up too — I’ve always been attracted to the blinking lights. Now I get to make some.
The real-time data we get is fascinating to watch and is constantly leading us in new directions to stay ahead of the blackhats. It will be interesting to see what other folks make of it.
Messages are passed through several layers of filters and tests to assure that maximum spam detection is achieved. Short Url
Perhaps, and I admit at the moment we’re not seeing a problem with referer. However others are consistently abused (bit.ly for example).